Intellligent locking platform
that maximises security and minimises lifecycle costs
One platform, many features
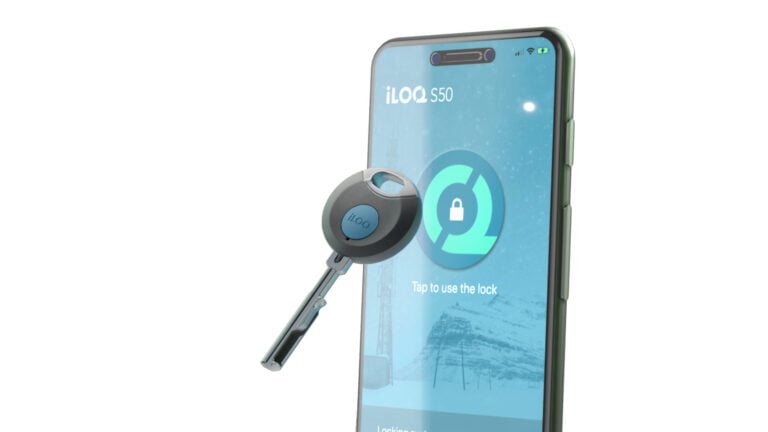
Thanks to opportunities offered by digitalization, you can now choose iLOQ’s key-based system, the mobile solution or even a combination of the two. With all access rights managed using the same software platform, iLOQ 5 Series fulfills the access management needs of all properties and user environments.

Battery-free access
With our key-based digital locking system, the power needed to confirm access rights and open locks comes from the motion of inserting the key into the lock. No batteries or cables are needed.
iLOQ cylinders replace existing cylinders with no modifications needed to doors or the infrastructure.
Outstanding benefits
Multiple
access possibilities
Digital key – can be used as a traditional key or with a reader
Smartphone key
Key fob
PIN code
Smarter, simpler administration
One flexible, scalable, easyto-use cloud-based SaaS platform.
Device-to-device communication between keys, locks, smartphones, readers and the software platform.
State-of-the-art security
Lost, stolen or unreturned keys are immediately blocked.
Expired keys have no access without administrative actions.
Confidential data protected with strong encryption
Streamlined operations
iLOQ’s standard, open application programming interface creates a multitude of integration possibilities.
Top security features
Data security
Customer databases are located on an ISO 27001:2013-certified cloud server
A log-in procedure (separate encryption of data) is needed for the client software installed on a customer’s PC that manages the system.
Each customer has their own SQL Server database, which is completely separate from other databases and isolated from the internet (communications through a web server).
Distributed security
A physical programming key is required for security-critical programming tasks – this is connected to the customer PC’s USB port.
Secure system architecture
All communications are protected with AES-256 encryption, and devices are securely programmed to the system using a programming key
Device security
Device identity is ensured by strong PKI-based (public key infrastructure) authentication.
There is mutual authentication (AES-256-encrypted) between the key and lock.
Functionalities at a glance
- Convenient management of locks, keys, sites
and users on a single platform - Access rights quickly and simply defined, updated and canceled
- Real-time views of access rights, access codes, keys, locks and readers on property floor plans
- Time restrictions can be set
- Possibility to overwrite automatic keys
- Lost or stolen keys can be immediately blocked
- Audit trail reports track use and help prevent misuse
- Quick and simple multi-site management
- 24/7 Internet connection
- Fast and easy installation
- Automatic backups and updates
- User-friendly graphical user interface
- High system security
- Powerful data encryption methods
- No need to invest in dedicated hardware and software IT
- No in-house server maintenance costs
- Device-to-device communication
- Secure login with a physical token
- API integration
iLOQ products