Why is unification the best growth path for your business?
The unification of physical security systems is a step towards greater operational efficiency and cost savings. In building a plan to achieve this, it is important to ask whether the company should:
- integrate systems.
- unify everything under one platform,
- or use unification as a first step and then add other integrated solutions to the platform at a later date.
To find the right answer to this question, it is important to have a good understanding of the difference between unification and integration.
Differences between unification and integration of security systems
UNIFICATION
A platform that seamlessly integrates all security applications into a single interface, where it will include:
- communication
- video surveillance
- intelligent video analysis
- automatic number plate recognition
- access control
- and much more
INTEGRATION
Integration is the combination of multiple independent systems.

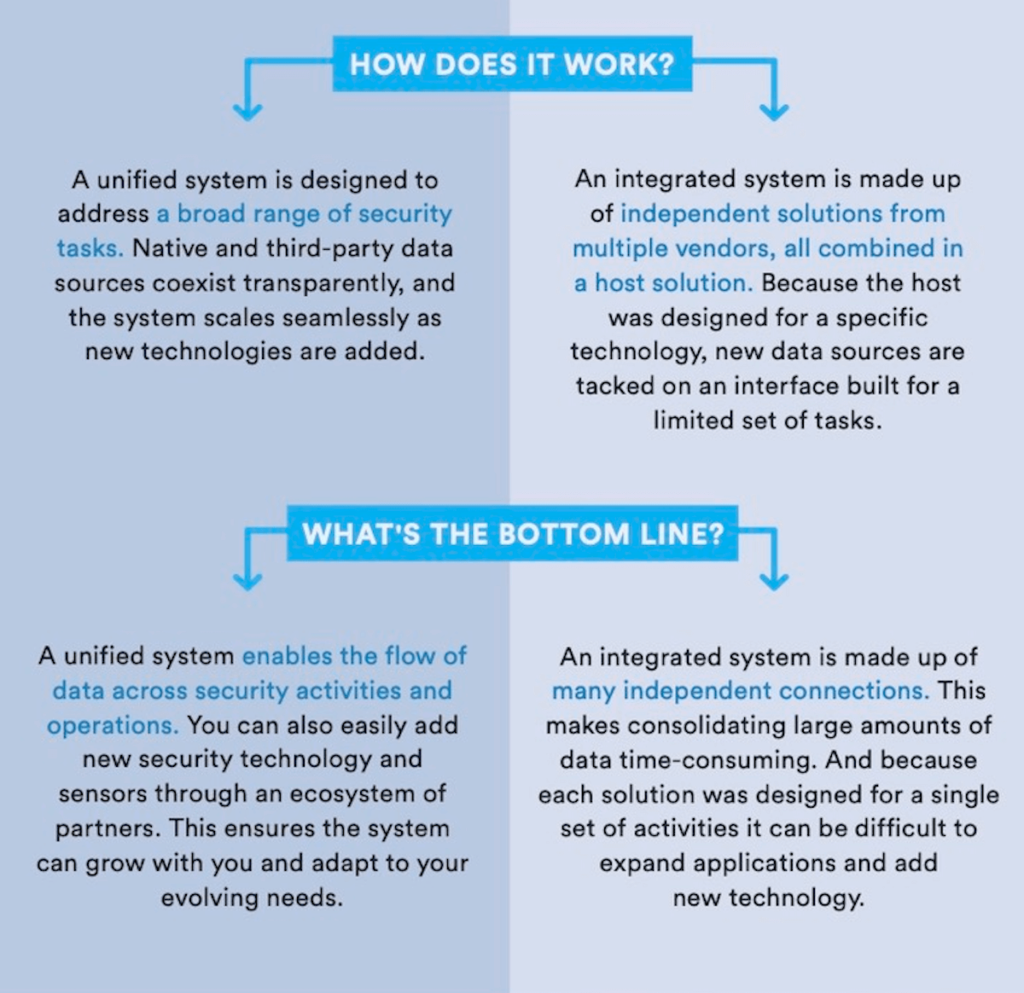
How does unification work and how does integration work?
UNIFICATION
The unified system is designed to perform a wide range of security-related tasks. Native and external data sources are brought together in one place and work together transparently. The system can be scaled up as new technologies are added.
INTEGRATION
An integrated system consists of independent solutions from multiple suppliers, connected via a host. A dedicated host built for specific technologies carries certain limited sets of tasks for new data sources that are added to the system.
Start with unification and integration will come later.
Every organisation and physical security installation is different. There is therefore no universal answer to the question of whether integration should be chosen over unification or the other way around in an implementation.
Unification, however, can provide deep connectivity between the main security systems, with benefits for the future. The unification strategy can also be complemented by introducing third-party integration into the same platform at any time.
This solution allows operators to use a single provider’s platform, while having access to all types of new technologies that best suit the organisation.
Two important issues when combining security systems.
A key success factor in combining unification and integration methods is the standardisation of open-architecture solutions. It enables greater interoperability between all solutions and makes the process of bringing new devices or systems onto a unified platform much easier and smoother later on.
With cybercrimes on the rise, supply chain risks should also be on target when deciding whether to integrate or unify systems. This is because when all systems are connected, the weakest link always creates the greatest vulnerability.
As the systems merge, the company will also begin to collect and process more data as part of its operations. Providing additional assurance that the business is protected will give owners peace of mind.
This is why it is so important to work with solution providers for whom data protection and privacy is a priority. Such due diligence will not only help fend off evolving cyber threats, but also supports the building of a strong cyber architecture on which to develop security and data operations.





